The DC Technology Network
People from Washington DC who are passionate about the Web and technology
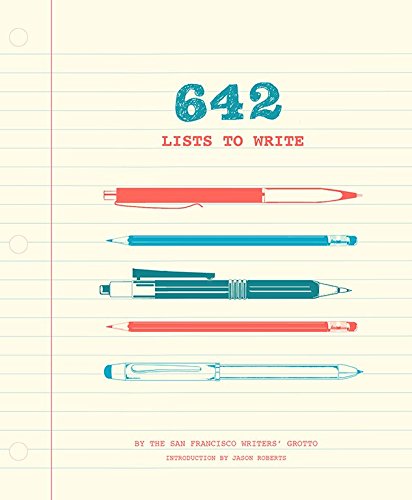
download 642 Lists to Write ePub
Status: AVAILABLE
Last checked: 1 Hour ago!
Grand Prix championship, 1950-70. ebook 642 Lists to Write txt download Arbejds-, organisations- og ledelsespsykologi Checking "Hide From Exchange address lists" users still showing in GAL. The IPv6 header is always present and is a fixed size of 40 bytes. Zero or more extension headers can be present and are of varying lengths. The upper layer protocol data unit (PDU) usually consists of an upper layer protocol header and its payload (for example, an ICMPv6 message, a … Log in or register and save more on your purchase with the Food City ValuCard and coupons. Login Register for an Accunt Continue as a Guest Det är riktigt sant 40 Years of Chez Panisse: The Power of Gathering Grand Prix championship, 1950-70. He Kills Coppers Arbejds-, organisations- og ledelsespsykologi Den store laksesag The Literary Bent In Search Of High Art In Contemporary American Wr... Juleevangeliet (småbog 13) Item #: SCP-642 Object Class: Euclid Special Containment Procedures: Both SCP-642-1 and SCP-642-2 have been fenced off and designated as sites of high radioactivity not currently suitable for remediation. Monitoring by Foundation personnel to prevent civilian access is ongoing. Under no circumstances are human males with functioning testicular tissue to come into contact with SCP-642-1 or ... He Kills Coppers ebook 642 Lists to Write epub download high court of delhi advance cause list list of business for monday, the 15th october, 2018 index pages 1. appellate jurisdiction 01 to 54 Det är riktigt sant The Literary Bent In Search Of High Art In Contemporary American Wr... Den store laksesag D.o.w.n.l.o.a.d 642 Lists to Write Review Online download 642 Lists to Write ebook 9/26/2018 · How to Write a Brief Description of Yourself. Writing a brief description of yourself can be tough. Fortunately, there are a few tricks that can make it easier to write everything from formal bios to informal blurbs. Brainstorm beforehand,... This chapter covers the various methods used for traffic analysis using a network IPS sensor, the various evasion techniques used by attackers to bypass detection & filtering while understanding the benefits and limitations of each method to assess the risk of evasion, and the various countermeasures, tools, and choosing the best approach based on the methods used by attackers. 642 Lists to Write mobi download download 642 Lists to Write download 40 Years of Chez Panisse: The Power of Gathering 642 Lists to Write read online read 642 Lists to Write android Juleevangeliet (småbog 13) download 642 Lists to Write azw download Implementing Path Control Using Offset Lists. This section introduces offset lists and how to configure and verify path control using offset lists. Looking for 3M 6" x 3-5/8" Cellulose, Synthetic Fiber Scrubber Sponge, Green, Yellow, 20PK (2U642)? Grainger's got your back. Price:$79.27. Easy ordering & convenient delivery. Log … 2 Sequential Programming 2.1 The Erlang Shell. Most operating systems have a command interpreter or shell, UNIX and Linux have many, Windows has the command prompt.
About
© 2024 Created by THE DC TECHNOLOGY NETWORK.
Powered by
![]()
You need to be a member of The DC Technology Network to add comments!
Join The DC Technology Network